Mid-January – February 2026
This report summarizes publicly disclosed cybersecurity-related incidents and policy developments in Japan during the above period.
1. Cybersecurity Incidents
Trend 1 | Ransomware
Nippon Medical School Musashikosugi Hospital (Feb 13) A suspected ransomware attack affected internal hospital systems. Approximately 10,000 patient records were reportedly exposed.
Hospitals in Japan are designated as critical infrastructure under the national cybersecurity framework.
GALA Yuzawa Ski Resort (Feb 12) A suspected ransomware attack on the lift ticketing system may have exposed personal data of up to 1,518 customers. The incident highlights that mid-sized regional operators are also reporting cybersecurity incidents.
Omnibus Japan (Feb 13) The company issued its fourth disclosure regarding a ransomware attack first detected in December 2025. The firm operates within Japan’s media and entertainment sector.
Advantest Corporation (Feb 19 disclosure) Advantest, a Tokyo Stock Exchange Prime-listed company and a major global manufacturer of semiconductor test equipment, reported detecting a ransomware attack on February 15 (JST). Investigation into the scope and impact remains ongoing.
Asahi Group Holdings (Feb 18 investigation report) Asahi Group Holdings, a multinational beverage company headquartered in Japan, published investigation findings related to a ransomware attack first disclosed in September 2025. Confirmed data exposure totaled 115,513 records.
Hosokawa Micron Corporation (Feb 2 detection / Feb 20 publication confirmation) The company confirmed a possible cyberattack. A ransomware group claimed exfiltration of 30GB of data, and partial publication was later confirmed.
>Context
The affected entities span healthcare, manufacturing, semiconductor supply chains, leisure services, and media. Japan’s corporate structure includes a high number of mid-sized firms and globally integrated manufacturers, many of which operate across complex supply chains. Public disclosures during this period indicate continued cross-sector exposure to ransomware activity.



Trend 2 | Cloud and Access Control Incidents
Mynavi Corporation (Feb 12)
Unauthorized access to a cloud service used by a major employment platform.
CyberAgent (Feb 12)
Cloud configuration error allowed unintended cross-user data visibility.
CAC Corporation (Feb 12)
Unauthorized access to a grants and donations management system.
Shinsia Co., Ltd. (Late January)
External unauthorized system access confirmed.
>Context
Cloud adoption in Japan has accelerated over the past decade, particularly among large enterprises and digital service providers. Several incidents during this period involved either external access to cloud-hosted systems or internal configuration errors. As in other jurisdictions, shared-responsibility security models continue to present operational challenges.
Trend 3 | Insider-Related Incidents
Nippan Group Holdings (Feb 13)
Former employee forwarded internal emails externally.
Manufacturing sector arrest (Feb 11)
Hiroshima Prefectural Police arrested a former employee on suspicion of copying engineering drawings to external storage.
Dai-ichi Life Insurance Group (Feb 12)
Information management issue involving staff seconded to an agency partner.
Japan Airlines baggage delivery service (Feb 10 disclosure / Feb 20 clarification)
Initially disclosed as suspected unauthorized access; later investigation determined contractor error and log alteration. No confirmed data exfiltration.
>Context
Japan’s corporate ecosystem is characterized by extensive subcontracting, secondment arrangements, and group-company networks. Several incidents during this reporting period involved individuals with legitimate access credentials, including former employees and contractors. Law enforcement has continued to pursue cases involving alleged technical data removal.
Trend 4 | AI-Related Developments
- In 2025, Japanese police arrested minors who had reportedly used generative AI tools in the development of unauthorized access tools.
- In August 2025, European security firm ESET disclosed a malware variant that incorporated real-time queries to external AI services.
- Japan’s Information-technology Promotion Agency (IPA) included AI-related cyber threats in its annual “Top 10 Information Security Threats 2026” — reflecting growing institutional recognition of AI as an attack enabler.
>Context
Japanese authorities and industry bodies have begun referencing AI-assisted techniques in both criminal investigations and threat reporting. IPA’s inclusion of AI-related risks reflects growing institutional awareness of generative AI’s potential misuse.

2. Policy Developments
Act on Prevention of Damage Caused by Unauthorized Acts against Critical Electronic Computers (Active Cyber Defense Legislation) Enacted May 16, 2025; promulgated May 23, 2025. To be implemented in phases within 18 months of promulgation (by November 2026), with full operational deployment targeted for fiscal year 2027. The legislation expands legal authorities to enable detection of and response to attack precursors on an ongoing peacetime basis. The National Police Agency will handle initial response; for sophisticated, organized attacks by foreign actors, a framework is envisioned in which the Self-Defense Forces also participate under Prime Ministerial directive and the command of the Minister of Defense.
National Cybersecurity Strategy Emphasizes public-private information sharing, early detection of attack precursors, and cross-sectoral coordination across critical infrastructure. The NCO (National Cyber Office), established on July 1, 2025 through the reorganization of NISC, serves as the central coordinating body. Note that “threat hunting” is not a statutory term; the activity is formally defined in legislation as the monitoring and analysis of communications information for the purpose of detecting attack precursors.
IT Vendor Accountability Guidelines A guideline aimed at clarifying the division of cybersecurity responsibilities between the government and critical infrastructure operators on one hand, and IT service providers on the other, is slated for finalization within fiscal year 2025. A draft — the “Guidelines on Required Roles of Cyber Infrastructure Operators (Draft)” — was released for public comment in October 2025, and work on finalization is ongoing. “IT Vendor Accountability Guidelines” is an unofficial, colloquial name.
JC-STAR IoT Security Labeling Scheme Launched March 25, 2025. Products are evaluated on a four-tier scale of one to four stars. Based on a Japan-UK memorandum of understanding concluded in November 2025, products certified at the ★1 level are deemed compliant with the technical requirements of the UK’s PSTI Act effective January 1, 2026 (mutual recognition applies to ★1 only). Discussions with the United States, EU, Singapore, and others are ongoing.
Counter-Espionage Legislation (Intelligence and Counter-Espionage Related Laws) A joint policy agreement between the LDP and Ishin, concluded in October 2025, explicitly calls for “prompt drafting and passage” of relevant legislation. Following the continuation of the same coalition government after the 2026 general election, Prime Minister Takaichi has expressed strong intent for early enactment, and the government officially confirmed the commencement of deliberations in February 2026. Reports indicate that an advisory panel of experts is to be established this summer, though the timeline for legislation remains undetermined and drafting work is in its early stages. It should be noted that this is a comprehensive legal framework encompassing defense and diplomatic secrets as well as foreign agent registration requirements, and is not limited to “economic espionage countermeasures.”
>Context
Japan has historically taken a relatively cautious approach to legal measures in cyberspace, placing significant weight on consistency with constitutional protections such as the secrecy of communications. Active cyber defense represents a major shift in statutory authority within that framework. The multiple policy measures described above are either in the process of phased implementation or remain under ongoing policy deliberation.

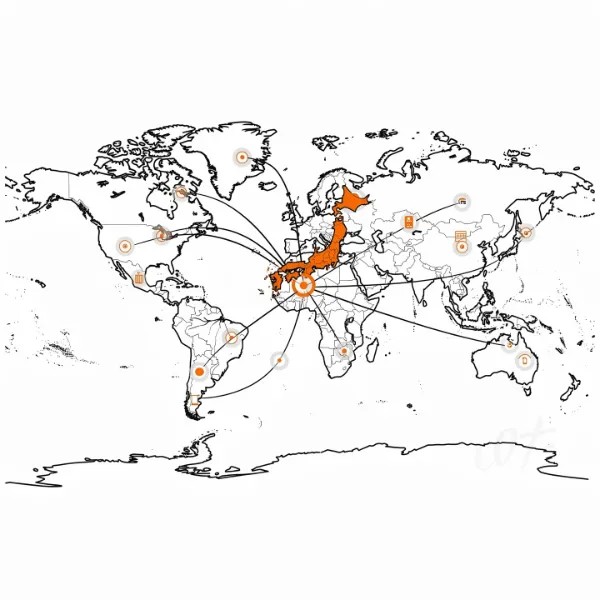
3. International Cooperation
- Continuation of Japan-U.S. cyber exercises and policy coordination (including the Japan-U.S. Cyber Defense Policy Working Group)
- Capacity building, information sharing, and joint exercises through the QUAD Cybersecurity Working Group
- JC-STAR mutual recognition with the United Kingdom (★1 level; effective January 1, 2026)
- Cyber cooperation with NATO (participation in Locked Shields exercises; cybersecurity designated as a priority area under the ITPP framework)
- Continued engagement with the EU and ASEAN on cybersecurity
>Context
Japan’s international cooperation in cyber policy is organized around two broad axes. The first centers on regulatory harmonization and mutual recognition with the United States, the EU, and NATO. The second focuses on capacity building, information sharing, and joint exercises with countries across the Asia-Pacific region through frameworks such as QUAD and ASEAN. On the JC-STAR front, mutual recognition with the United Kingdom has been realized, and negotiations with Singapore and other regional partners are ongoing; however, compared to the regulatory harmonization achieved with Western counterparts, engagement at the regional level remains a work in progress. Taken together, these efforts form part of a broader international movement toward greater interoperability of digital security standards.Continued Japan–US cyber exercises and coordination activities.
Overall Snapshot
Public disclosures from mid-January through February 2026 reveal incidents across multiple sectors and organizational types, while concurrent policy developments point to continued expansion of Japan’s cybersecurity governance framework — with implementation milestones running through late 2026.
Information is based on publicly available sources as of February 28, 2026.
[JICSS Exclusive]
Expert Commentary By:
Nate Snyder / JICSS Special Advisor
Mobilizing Global Knowledge: Defining Japan’s Authentic Cyber Path
I served as a senior national security official in Obama-Biden and Biden-Harris Administrations. In those roles I addressed numerous threats that the U.S. and her allies faced. These threats ran the gamut from foreign and domestic terrorists and their use of technology to carry out attacks, to critical infrastructure protection and ensuring that U.S. communities and allies across the globe had the ability to identify and mitigate threats on an ever-changing landscape.
Doing so meant that you needed to consistently assess a dynamic and sometimes asymmetric environment, but most importantly, that adaptation is a must. Sometimes that meant making tough decisions, breaking out of comfort zones by taking risks, asking tough questions, pushing transformation within established institutions, forming unlikely partnerships, and at times even failing. I have joined JICSS at what feels like a crucial moment for Japan, and I am hopeful that I can take those lessons and impart them on a trusted ally.
Since joining JICSS in 2025, I’ve been closely immersed in Japan’s cybersecurity landscape. As covered in our curated news aggregation and analysis, the constant stream of security incidents has only intensified since the start of 2026. Given this environment, I feel there is special significance in compiling and delivering valuable curated information and insights through the JICSS platform. I see this also as a great opportunity to engage with our readers, subscribers, and members through this effort as a very positive but necessary undertaking.
Japan has always been exceptional at innovation—refining, perfecting, and doing things better than anyone else. But today’s cybersecurity challenges are moving faster than traditional approaches can handle. The threats are real and growing, from critical infrastructure vulnerabilities and state and non-state threat actors (PRC, DPRK, RUS), to regional security challenges that affect everyone from consumers to government.
Japan’s greatest transformations—the Meiji era, the post-war miracle—happened when global expertise met Japanese leadership and dynamism. Not by abandoning what makes Japan special, but by amplifying it. That’s exactly what we’re building at JICSS.
Our mission is straightforward but urgent: partner with Japanese leaders to develop cybersecurity solutions that are both world-class and authentically Japanese. Solutions that tackle real threats while respecting the culture and values that matter. We’re not here to import foreign models—we’re here to help mobilize the best global knowledge in service of Japan’s security and resilience.
This charge we have at JICSS is no small undertaking. It is clear that the norms and long established conventional wisdom are changing in the region as well as globally. We are seeing the cyber attack surface change overnight, new threats and trends emerge, but also new opportunities to explore and new partners to enlist. This is very much an introduction, however, I am looking forward to working with the JICSS community to shed light on how we can take these challenges on together. I am also hoping that with your participation we will be able to drive this vital conversation. So, please watch this space, we will have more analysis, information, expertise, and engagement to share. I am looking forward to it. Onward.
Disclaimer:
This report is based on publicly available information as of February 28, 2026. Information may be subject to change as investigations and policy developments continue. The content is provided for informational purposes only.