Organizers: JICSS / Keio Univ. CCRC / TenguSec
Date: Nov.13, 2024
Venue: Roppongi, Tokyo Japan
1. Overview
This year’s inaugural TenguCon, held on November 13th, 2024, brought together a diverse array of members in the cybersecurity community. It hosted 110 participants, including 68 general attendees, 26 affiliated members, and 16 esteemed speakers. The event integrated technical expertise with critical policy discourse, highlighting three main tracks: InfoSec Community, Policy & Cybersecurity, and specialized Villages dedicated to car hacking, malware analysis, and physical security awareness.
2. Keynotes and Sessions
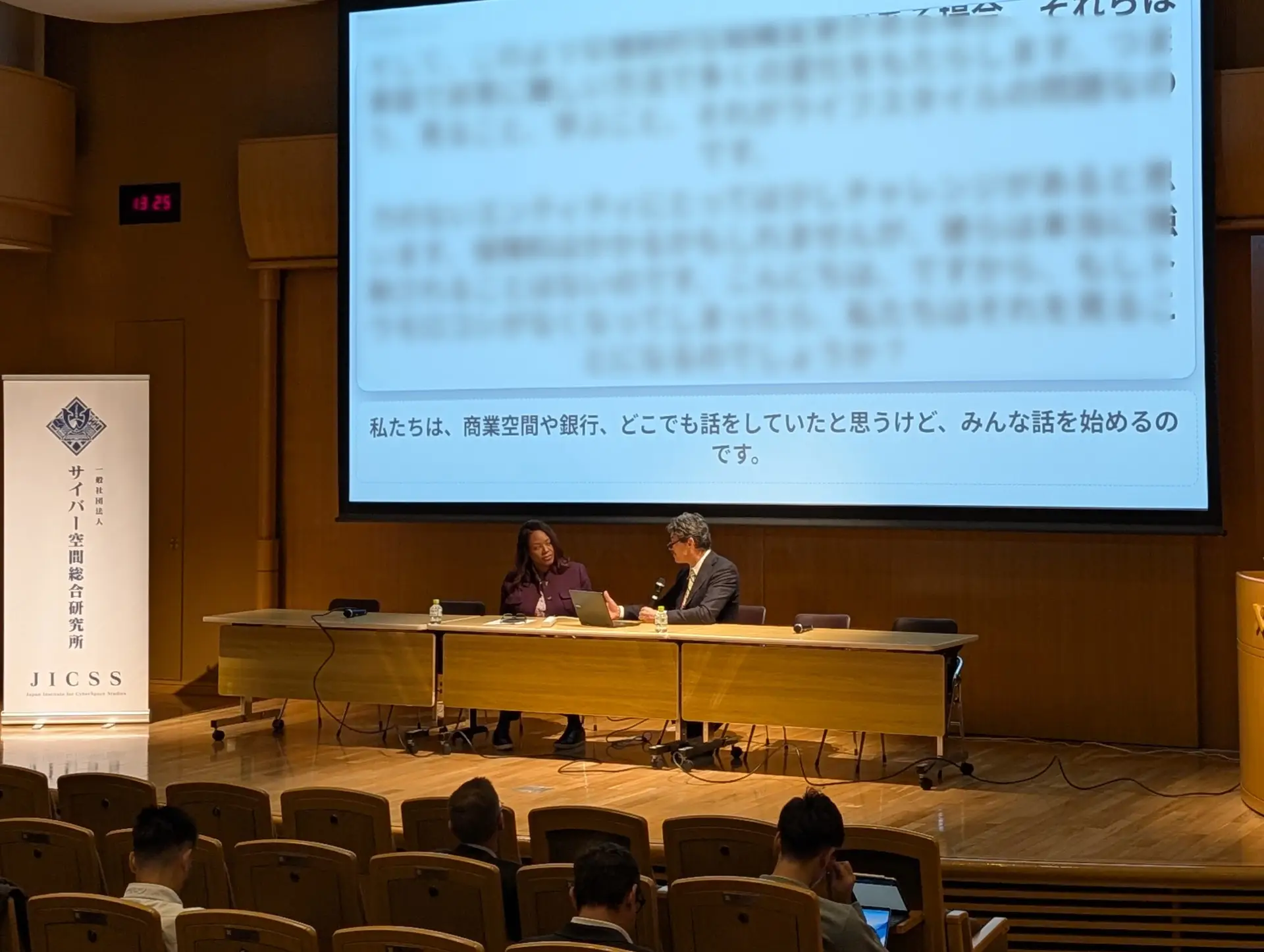
Opening Keynote: U.S.-Japan Cybersecurity Cooperation
Daniel C. McCandless, Counselor for Environment, Science, Technology, and Health at the U.S. Embassy in Tokyo delivered the opening keynote address. He addressed predicaments that the United States and Japan face in cybersecurity and emphasized the strategic importance of fostering collaboration between technical experts and policymakers. Key themes included critical infrastructure vulnerabilities and threats posed by state-sponsored actors, exemplified by groups such as Lockbit. Counselor McCandless highlighted opportunities for joint initiatives with Japan and other partners, including the annual U.S.-Japan-EU Industrial Control Systems (ICS) Cybersecurity Week and collaborative efforts between DHS/CISA and JP-CERT/NISC.
Lunch Session: Evolving Compute Paradigms and National Security
Law and policy experts focused in the lunch session on the intersection of emerging computational technologies and their implications for national and economic security. Discussions explored the evolution of edge to cloud hybrid environments and the challenges of integrating modern security frameworks with legacy systems. The session also examined the evolving balance between compliance-driven and operational security requirements and strategies to enhance security effectiveness in distributed systems.
Central to the dialogue were issues surrounding identity and data management. The speakers elaborated on the distribution of responsibility in identity verification, the need to minimize redundant sensitive data collection, and the pivotal role of government in offering authoritative identity services. Furthermore, the session emphasized the growing importance of protecting critical infrastructure, drawing lessons from automotive security and examining European approaches to digital identity and trust.
Presentations and Discussion Highlights
The conference hosted a series of distinguished speakers who shared their expertise on cutting-edge topics. Highlights included Hari Hursti’s analysis of protecting critical infrastructure in the AI era, YTCracker’s exploration of wireless security challenges, and Billy Wong’s in-depth examination of Chinese cyber threats. In addition, the agenda featured sessions on automotive security, container security, and privacy advocacy, ensuring a comprehensive overview of contemporary cybersecurity challenges.
InfoSec Community Track Presentations
- Wireless world domination
- You can’t detect me if you don’t know I exist
- falco – Container intrusion detection system
- Abusing intended feature and bypassing facial recognition
- Steganography in the wild
- Phishing and social engineering: Unveiling the dark tactics of cyber deception
- Exploring Chrome
- DNSForge – responding with force
- How I built a personal brand to build trust and influence at scale
- Unmasking Chinese stealthy threats- lessons learned from Ivanti Zero-Days
- Evolving compute paradigms and national security
- My journey in Google bug bounty
- Automated media fuzzing for autoplay in car information systems
Policy & Cybersecurity Track Presentations
- Protecting Critical Infrastructure in the Age of AI
- Data Privacy Advocacy 101 – How to Fight for Your Law
- You are an Ethical Hacker. What next?
- The Looming Ocean: The Singularity and Cyber
Specialized Villages Features
The villages featured four concurrent specialized areas:
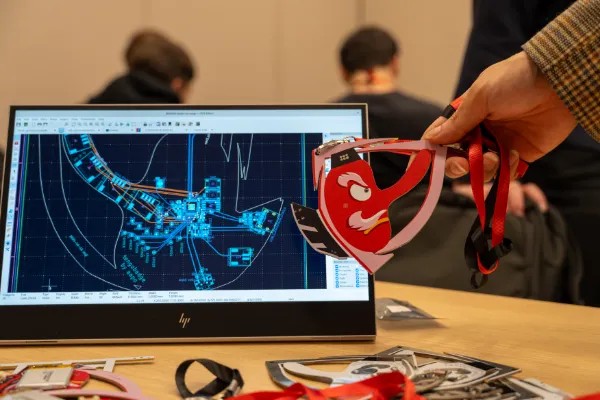
- Car hacking village: Focused on automotive security challenges and OTA update security
- Malware village: Examining current threats and analysis techniques
- Physical security awareness: Practical demonstrations and training
- Most creatively named DTF in history
3. Technical Highlights
Automotive Security
- Advanced testing methodologies for vehicle infotainment systems
- Security architectures for ADAS systems
- OTA update security frameworks
- Integration of ISO 21434 standards
- Supply chain security considerations
Mobile and Operating System Security
- Android security research methodologies
- Bug bounty program insights
- Reverse engineering techniques
- Mobile OS vulnerability analysis
- Tool development for security research
Infrastructure Security
- Container security implementation strategies
- Cloud-edge hybrid environment security
- Critical infrastructure protection frameworks
- IoT security architecture
- Identity and access management in distributed systems
Emerging Threats
- Advanced persistent threat analysis
- Zero-day vulnerability research
- Social engineering evolution
- Wireless security challenges
- AI-related security implications
4. Next Steps
TenguCon 2024 adds a pivotal platform for advancing cybersecurity discourse in Japan. By integrating technical expertise, policy considerations, and practical implementation strategies, the event emphasized the necessity of international collaboration to confront evolving cyber threats and safeguard critical infrastructure. The success of this inaugural conference lays a robust foundation for future engagements in the cybersecurity domain.
JICSS will continue to work with TenguSec as well as CCRC of Keio University and other cybersecurity focused organizations to bring together experts from industry, academia, and government to generate practical policy solutions and build consensus for action on cybersecurity.