Date: July 29, 2025
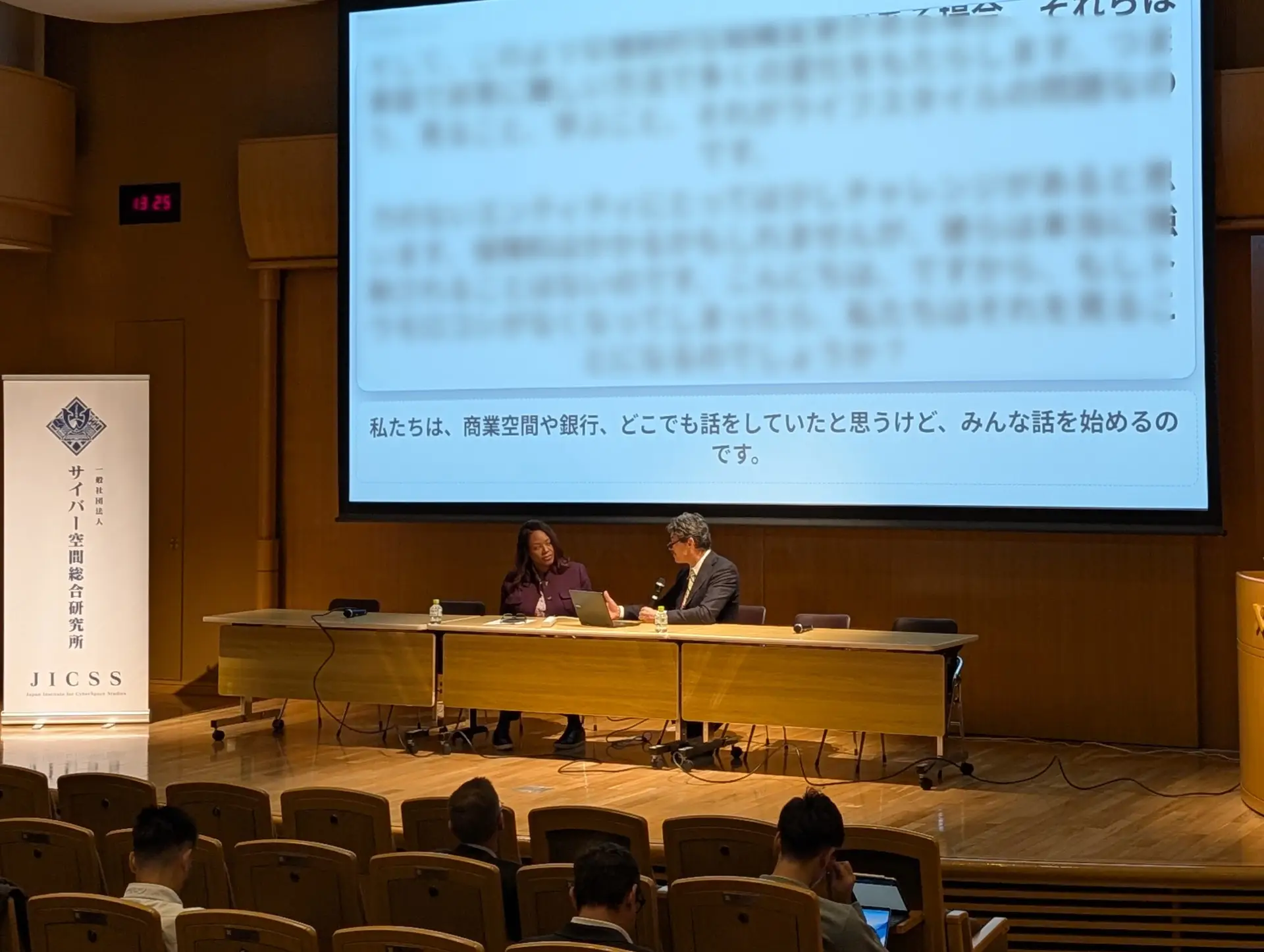
Location: JICSS Headquarters, KR II Ginza Building, Tokyo
Event Overview
The Japan Institute for Cyberspace Security Studies (JICSS) successfully hosted its Q3 2025 seminar featuring a comprehensive presentation on Japan’s Active Cyber Defense (ACD) framework and opportunities for enhanced Japan-US cybersecurity cooperation. The event was held at JICSS headquarters on July 29, 2025, from 19:00 to 20:50 JST, followed by a networking reception.
The seminar was conducted under Chatham House Rules to encourage frank and open dialogue among participants.
Distinguished Guest Speaker
The seminar featured Ms. Gloria Glaubman, Senior Cyber Adviser at the U.S. Embassy in Japan, as the keynote speaker. Ms. Glaubman was recognized for her pivotal role in revitalizing cybersecurity understanding and fostering bilateral cooperation between Japan and the United States. The seminar marked Ms. Glaubman’s final engagement in her official capacity at the Embassy.
Participants
The seminar brought together a distinguished group of cybersecurity leaders from government, military, industry, and academia, representing both Japanese and international organizations. Participants included representatives from U.S. government agencies, major technology companies, defense contractors, and academic institutions, participating both in-person and online.
Discussion Highlights
Ms. Glaubman delivered an insightful presentation examining the current state of cybersecurity developments in Japan and exploring pathways for strengthened international cooperation. Her presentation drew on extensive experience working with Japanese cybersecurity stakeholders and provided valuable perspectives on the evolving threat landscape.
Major Themes Discussed:
1. Structural Differences in US-Japan Cybersecurity Operations
The discussion highlighted fundamental differences in the operational structures between U.S. and Japanese cybersecurity frameworks. These structural divergences present challenges to seamless bilateral cooperation and information sharing. However, both nations have benefited significantly from shared intelligence and lessons learned through the Five Eyes alliance framework.
2. Japan’s Active Cyber Defense Law
Participants examined Japan’s new ACD legislation, representing a major evolution in the country’s cybersecurity posture. The implementation timeline is projected at 2-3 years, with significant attention required to reconcile differing operational approaches between Japanese and U.S. frameworks, particularly regarding transparency and information sharing protocols.
3. Security Clearance and Classification Challenges
A critical barrier to enhanced cooperation was identified in Japan’s security clearance system, which is not yet fully aligned with Five Eyes standards. This misalignment creates obstacles to intelligence sharing and joint operations. Additionally, trust and coordination issues between different Japanese agencies—including the Ministry of Defense (MOD), National Police Agency (NPA), and the newly established National Cybersecurity Office (NCO)—require attention.
4. Cloud Adoption and Regulatory Constraints
The discussion addressed regulatory barriers to cloud adoption in defense cooperation contexts. Private cloud solutions were suggested as potential workarounds for current regulatory constraints while maintaining necessary security standards.
5. Critical Role of Private Sector Engagement
A consensus emerged that private enterprise involvement in both cybersecurity operations and education will be paramount moving forward. Due to limitations in government resources, knowledge, and capabilities, private sector partnerships will remain a strategic priority for both nations. The development of human capital and workforce capabilities was identified as a critical bottleneck requiring immediate attention.
6. Practical Implementation Challenges
Participants emphasized the need for pragmatic, solution-focused proposals with clear timelines and problem statements. Moving from policy to practice requires actionable frameworks and concrete implementation plans that can be executed within realistic timeframes.
Action Items and Next Steps
Following the seminar, JICSS has identified several concrete action items to advance cybersecurity cooperation and understanding:
- White Papers on Private Sector Integration: JICSS will circulate draft white papers to all members for input and feedback, focusing on effective models for private sector involvement in national cybersecurity initiatives.
- NCO Organizational Mapping: JICSS will develop and distribute a comprehensive mapping of the National Cybersecurity Office (NCO) structure and agency roles. This resource will clarify relationships with existing government agencies and help stakeholders understand the evolving Japanese cybersecurity landscape, promoting more effective cooperation.
- IP Asia Meetings Participation: JICSS will facilitate member participation in the “IP Asia Meetings” held weekly on Mondays by Keio University’s Cyber Civilization Research Center (CCRC). These meetings provide opportunities for enhanced information exchange and robust dialogue on Internet society development.
- October 2025 Conference Coordination: JICSS will coordinate participation in the Keio University security conference scheduled for October 2025, facilitating continued dialogue among stakeholders.
- Private Intelligence Sharing Mechanism: JICSS will continue its ongoing initiative to develop a private Information Sharing and Analysis Center (ISAC) to enhance threat intelligence sharing between industry participants.
- Deep-Dive Discussions: JICSS will organize additional focused discussions on private sector involvement, serving as a bridge between public and private sectors to facilitate effective engagement models.
Key Takeaways
- Japan’s ACD law represents a significant milestone in the nation’s cybersecurity evolution, though successful implementation will require sustained effort over a 2-3 year timeline
- Structural and operational differences between U.S. and Japanese approaches necessitate careful coordination and mutual understanding
- The private sector will play an indispensable role in building Japan’s cyber capabilities and operational capacity
- Human capital development remains the most critical bottleneck and requires immediate strategic attention
- Actionable, timeline-driven proposals with clear problem statements are essential for moving from policy to practice
- As a trusted bridge between government and industry, JICSS is uniquely positioned to facilitate the partnerships necessary for enhanced cybersecurity cooperation
Looking Forward
The seminar underscored JICSS’s mission to foster common understanding of cybersecurity structures and terminology, thereby promoting cooperation and development across sectors and borders. By bringing together diverse stakeholders and facilitating substantive dialogue, JICSS continues to advance its role as a thought leader in cybersecurity policy and practice.
JICSS extends its sincere appreciation to Ms. Gloria Glaubman for her outstanding contributions to Japan-US cybersecurity cooperation and wishes her continued success in her future endeavors.